Building AI Knowledge Bases That Actually Work with Claude
Every time you start a new conversation with Claude, it starts completely fresh. No memory of last week, no knowledge of your workflows, no context unless you provide it. In this post, I walk through how to build a structured personal knowledge base that Claude can actually use: the right file formats, how to organise your folders, how to write documents Claude can navigate quickly, and how to connect everything through Google Drive so Claude searches it automatically.
I got tired of 47 browser tabs. So I built BrowserSentinel.
Every investigation starts the same way: 40 tabs, no structure, no audit trail. BrowserSentinel is the tool I built to fix that. Local-first, no cloud, no account. Case management, 166+ OSINT tools, embedded investigation browser, and AI integration. Free for personal use.
When the Tide Turns: Applying Security Principles to Your Career
Career disruption is inevitable, but for security professionals, so is the instinct to prepare for it. This post, draws a direct parallel between the frameworks we use to protect organizations and the mindset we need to protect our own careers. Whether you're navigating a layoff, a company pivot, or an uncertain job market shaped by AI transformation, the principles of preparedness, mitigation, and lessons learned. This is a candid, practical guide to staying ahead, professionally and personally when the tide starts to turn.
How Risk Management and Threat Intelligence Should Actually Work Together
Most organisations run Risk Management and Threat Intelligence as separate disciplines. They shouldn't. Here is what happens when you close the loop between them
From Agent-on-Agent Fraud to Autonomous AI Attacks: The Next Escalation
In 2024, the big worry was humans being fooled by AI. By 2026, a new threat is emerging: Agent-on-Agent (AoA) fraud. As more organizations rely on AI agents for procurement, treasury, and customer service, the traditional “perimeter of trust” is disappearing. Fraud isn’t just human-to-machine anymore. Now, it can happen machine-to-machine, where one autonomous AI agent tricks another.
When Your AI Agents Start Tricking Each Other
In 2024, the big worry was humans being fooled by AI. By 2026, a new threat is emerging: Agent-on-Agent (AoA) fraud. As more organizations rely on AI agents for procurement, treasury, and customer service, the traditional “perimeter of trust” is disappearing. Fraud isn’t just human-to-machine anymore. Now, it can happen machine-to-machine, where one autonomous AI agent tricks another.
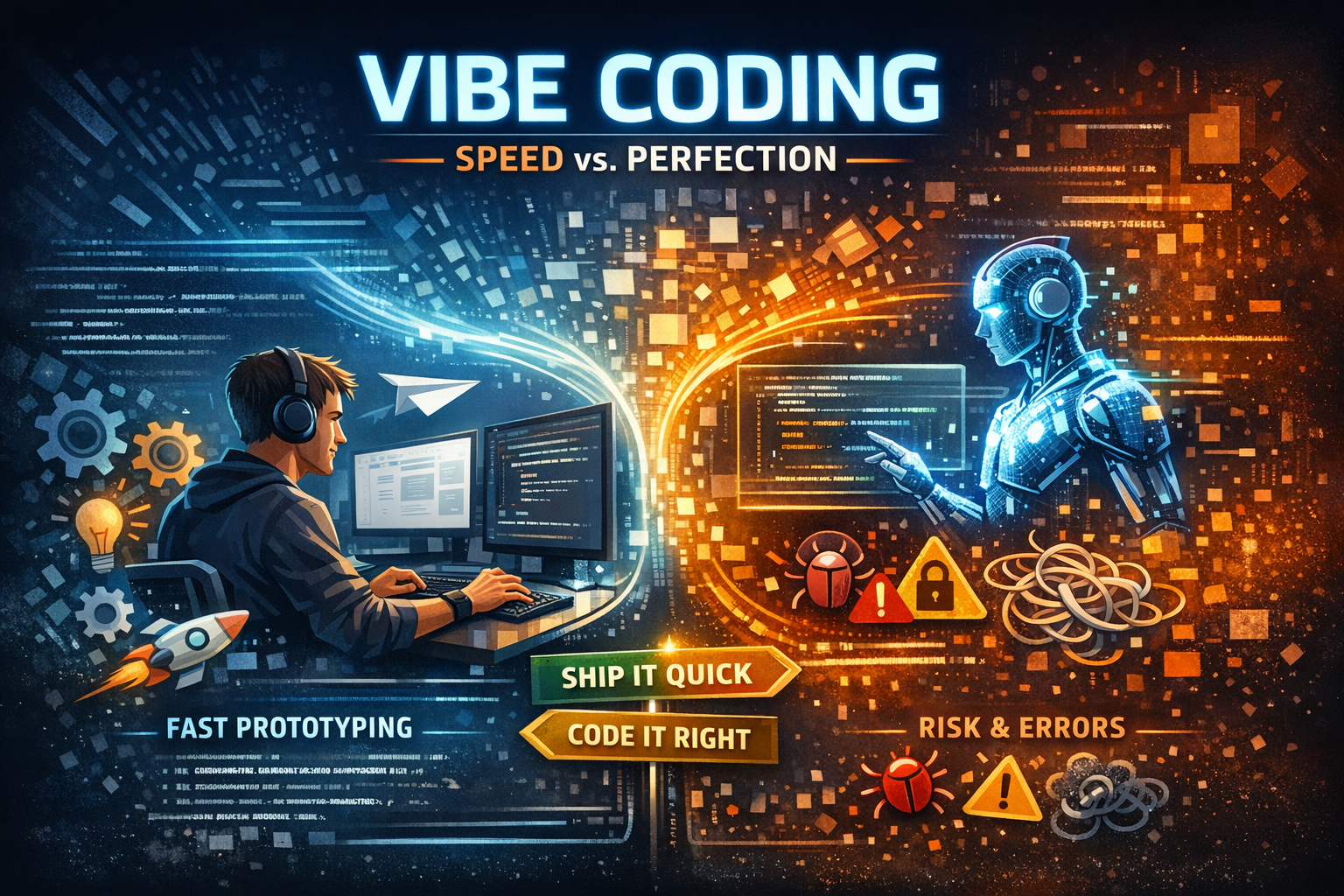
Vibe Coding: Hype, Reality, and What It Actually Means
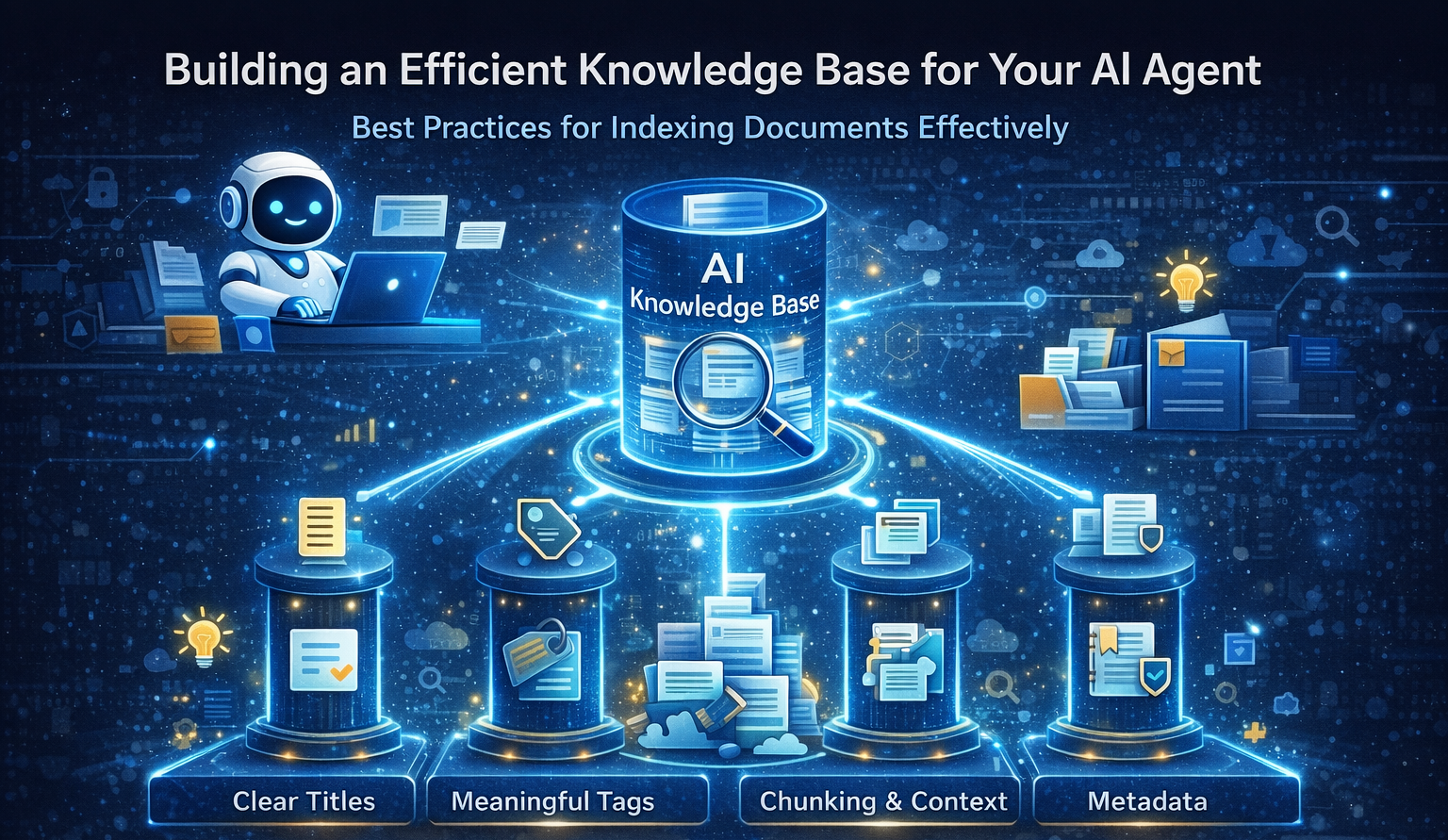
Most AI projects don’t fail because of the model — they fail because the knowledge base behind it is messy, outdated, or impossible to retrieve from. Before embeddings, vector databases, or fancy architectures, the real work starts with how your documents are written, structured, and indexed.
In this piece, I break down what it actually means to prepare a knowledge base for AI agents in security, compliance, and risk environments. We’ll look at when indexing really matters, how to structure documents so AI can retrieve answers faster, and why clear titles, meaningful tags, and proper chunking often outperform more complex solutions.
I also share practical examples, a simple readiness checklist, and lessons learned from building AI systems that had to stand up to audits and incident reviews — not just demos.
If you wouldn’t trust a document in an investigation, your AI shouldn’t either.
Building AI Knowledge Bases That Actually Work
Most AI projects don’t fail because of the model — they fail because the knowledge base behind it is messy, outdated, or impossible to retrieve from. Before embeddings, vector databases, or fancy architectures, the real work starts with how your documents are written, structured, and indexed.
In this piece, I break down what it actually means to prepare a knowledge base for AI agents in security, compliance, and risk environments. We’ll look at when indexing really matters, how to structure documents so AI can retrieve answers faster, and why clear titles, meaningful tags, and proper chunking often outperform more complex solutions.
I also share practical examples, a simple readiness checklist, and lessons learned from building AI systems that had to stand up to audits and incident reviews — not just demos.
If you wouldn’t trust a document in an investigation, your AI shouldn’t either.
How AI is Connecting Analysis, Threat Hunting and Cloud Investigations
Security, fraud, and cybersecurity teams face a growing challenge: protecting increasingly complex environments shaped by cloud adoption, AI, and IoT, while threats evolve faster than ever. Bad actors are also leveraging AI to scale and accelerate their attacks.
AI is no longer optional, it has become essential. When used correctly, AI can improve security posture and operational efficiency, not by replacing people, but by connecting critical security functions and breaking down silos.
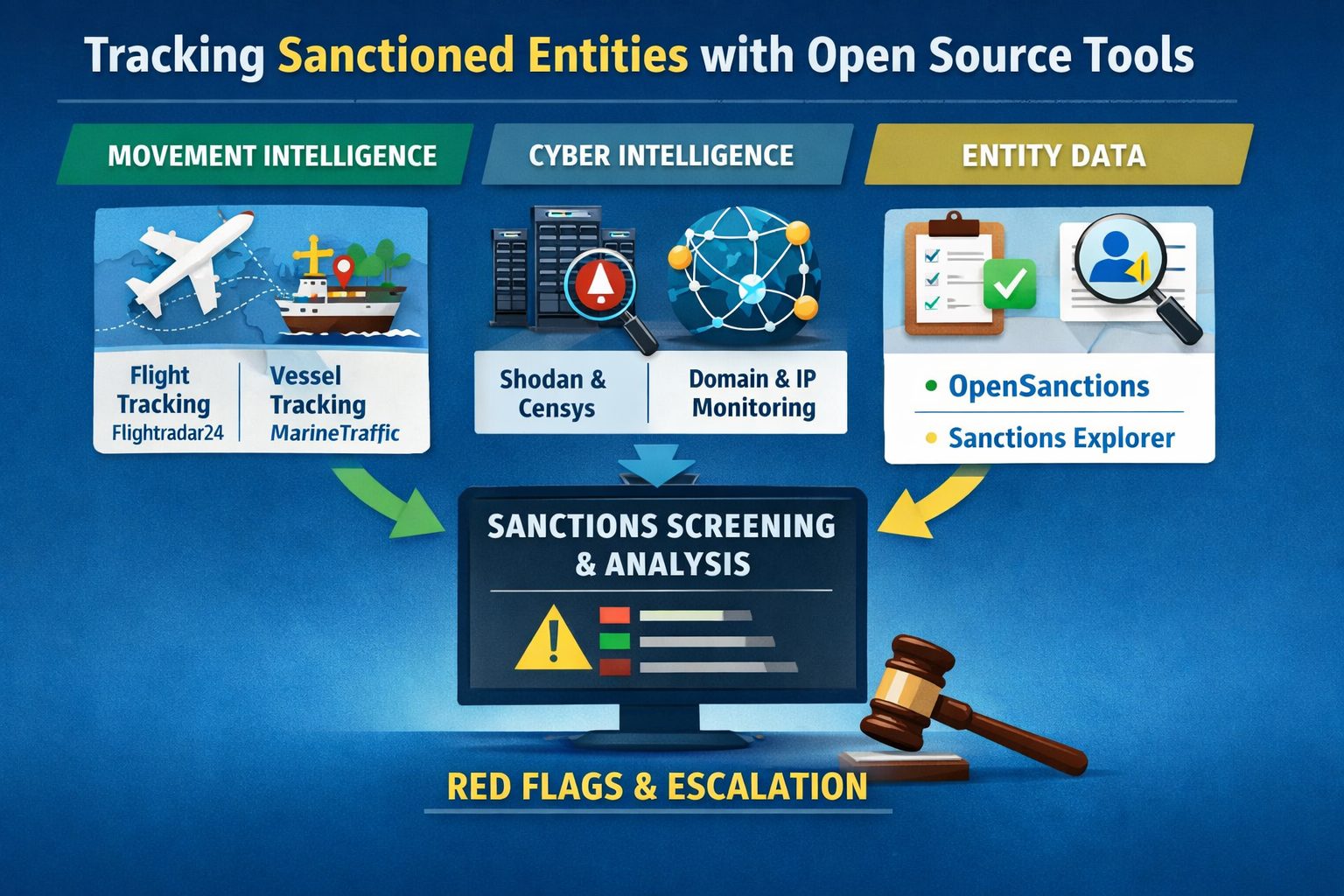
How to Use Open‑Source Tools to Monitor Sanctioned Entities and Individuals
Open source tools—flight and vessel trackers, internet scan engines, and aggregated sanctions lists—can surface early, actionable signals for sanctions monitoring when layered together, documented, and used within legal limitations.
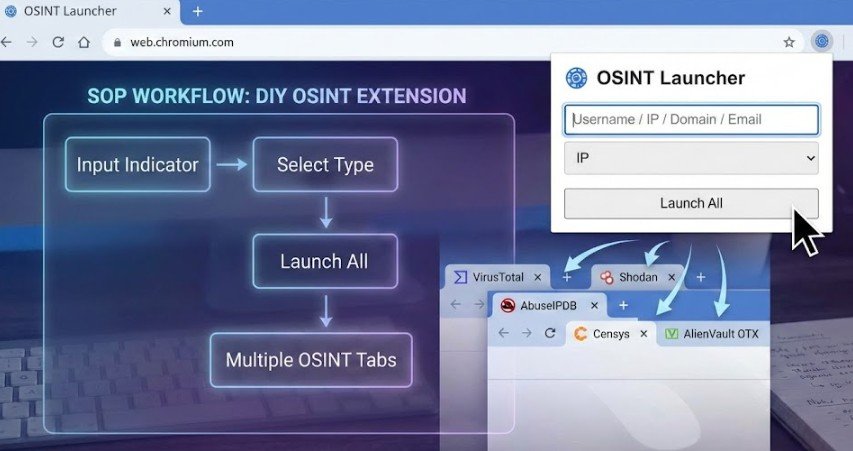
Tab Fatigue? Build Your Own OSINT Launcher Extension
Build your own OSINT browser extension
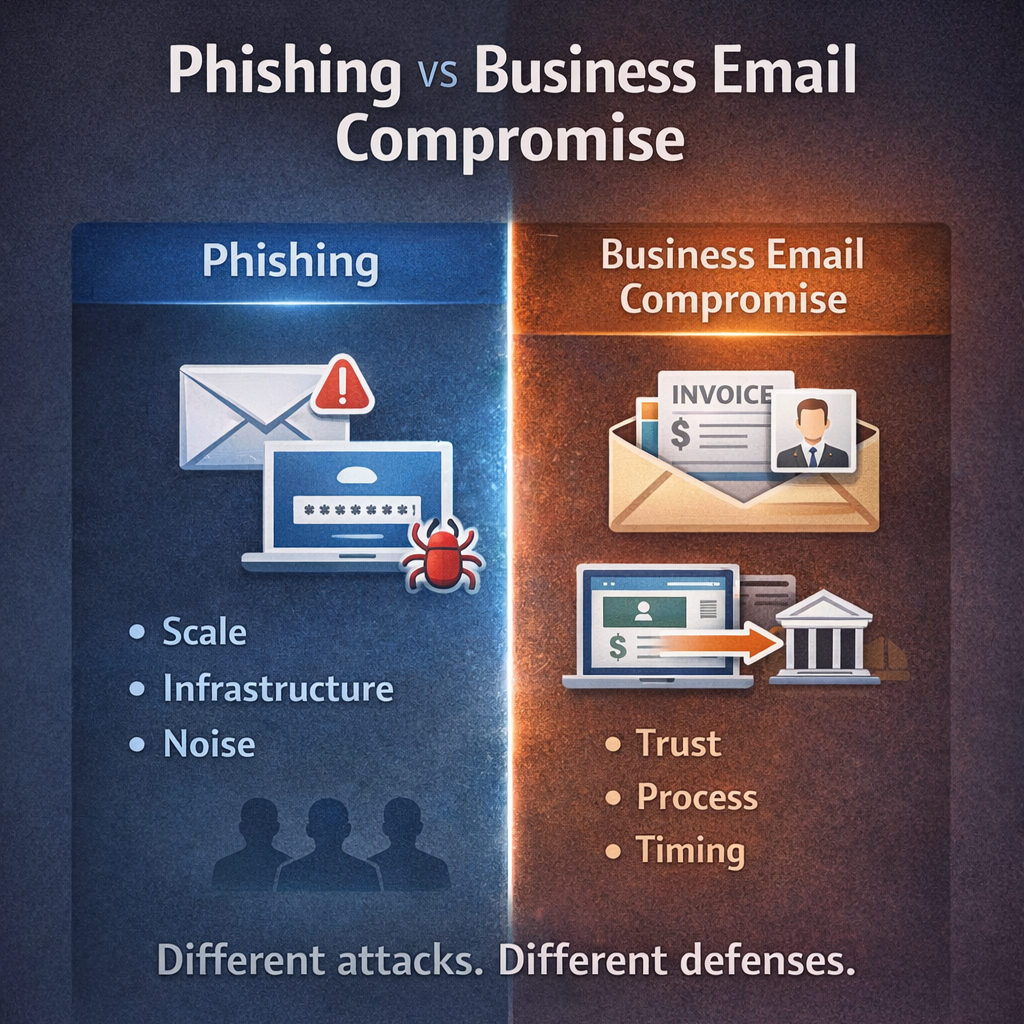
Differences between Business Email Compromise and Phishing or Spear Phishing
Understand the difference between Phishing and Business Email Compromise
Risk vs Threat: A Practitioner’s View
Understand the difference between risk and threat in cybersecurity, cloud investigations, fraud, and threat intelligence and why it matters to the business.
Fraud vs. Abuse: Why the Difference Matters
Understand the difference between fraud and abuse in cloud platforms.